London Stack Smashers is a fairly new social event that tries to gather IT Security professionals and enthousiasts around this subject.
After being there for doing a short presentation for Shellter, it’s time to provide some feedback.
The organizers were very kind and it is clear that they are trying their best to set everything up. However, I didn’t like much the space where the event took place.
That being said, it is quite obvious that sponsors would be more than welcome.
Overall, I can see that there is some passion towards this event, but the motivation behind it is not so clear to me yet.
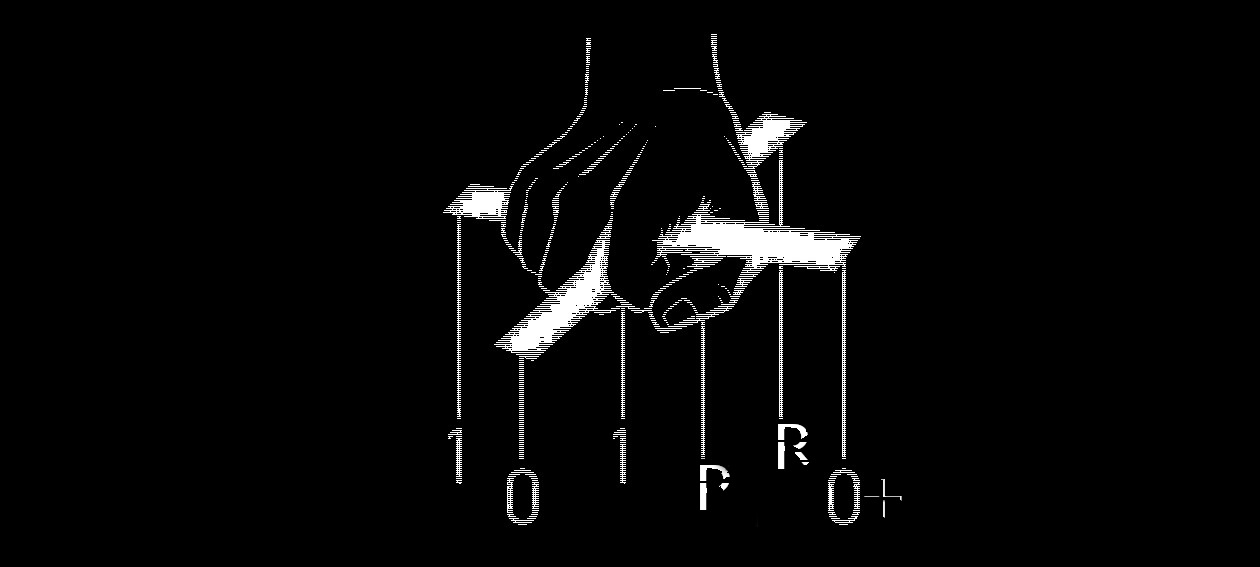
Anyway, going back to Shellter, I hope that people enjoyed watching it in action and learning a little bit more about its internals and concepts behind it.
During the presentation, I tried to do an extra demo including the ‘Dynamic Thread Context Keys’ feature, which is an experimental feature of Shellter introduced in version 4.0. That particular demo failed* just because of this specific feature. This gave me some extra food for thought, and for that reason in the upcoming version I will introduce some modifications that will hopefully make it as reliable as possible.
This is an awesome feature, and it is really worth it to spend some time on it and hopefully make it an official feature rather than experimental.
To be honest, that was the first time that feature failed me, but if there is a chance to make it more reliable, I will definitely work towards that path.
There is a lot more to come with the upcoming versions of Shellter, and as I always promised every single update or modification is for making this whole thing as epic as possible.
Thank you all for using Shellter for real; even those that upload samples to VirusTotal from time to time. When you make something, you need to have the balls to test it as hard as possible. If you don’t believe in what you do, then drink your milk and go to bed.
*Update: After double checking this at home, I verified that indeed this was not really a mistake of Shellter itself. The issue was caused by a slight thread context modification between running the target application in Wine (where we used Shellter for injection), and then running the infected application in a Windows host.
It was a coincidence to pick up an injection location where the EDI register pointed to the entry point just because of a pointer leak during process loading in Wine, while in the Windows host EDI at the same execution point was zero.
However, I am still testing some modifications in the usage of Dynamic Thread Context Keys in order to avoid other possible issues in the future.
Cheers,
kyREcon