Latest version of Shellter, is now available to download.
I promised that every single feature that is added, will be useful and epic, and I will be always working towards that promise.
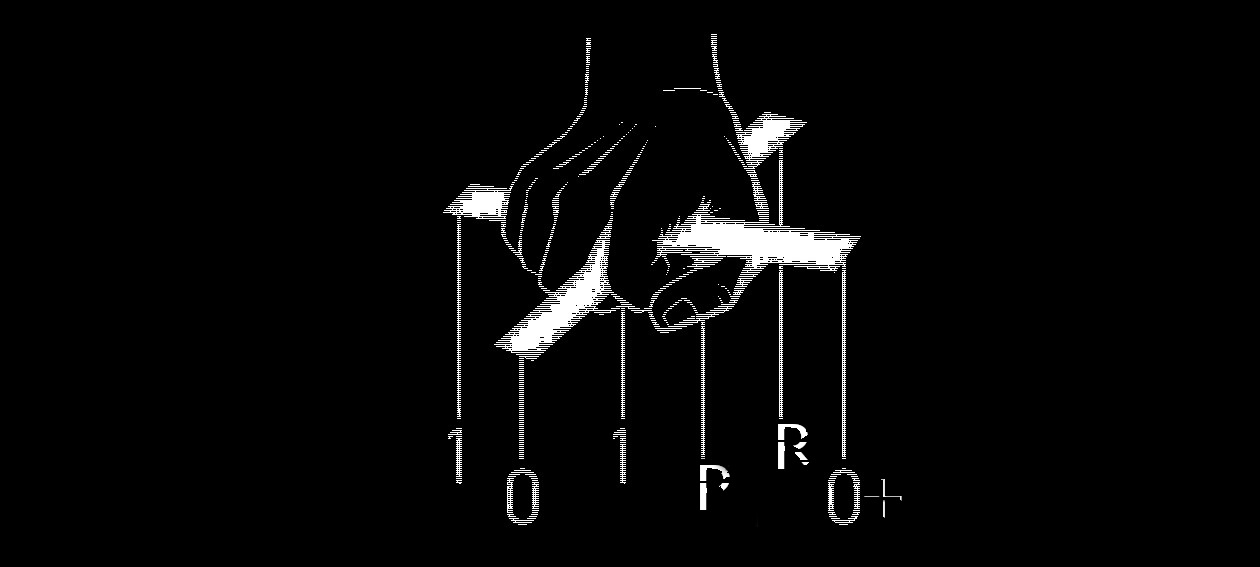
Indeed, Shellter V finally brings the RedTeam functionality that many people were asking for. This new feature comes under the name of Stealth Mode and allows Shellter to preserve the original functionality of the application while the tool itself doesn’t compromise it’s main concept, which is dynamic PE infection.
Furthermore, the design of Stealth Mode allows to re-infect multiple times the same PE binary. This means that you can inject all the payloads that you want to execute at the target host at once.
These will be executed independently one from the other, so if one fails to deliver because for example didn’t manage to connect back to you using the port you specified, that will not affect the rest of them.
You can combine any 32-bit payload you want. You can inject an add_user payload combined with reverse_tcp/http/https, and so on…
However, before you start playing with Stealth Mode it is recommended that you read about it in the readme.txt document that comes along with every new release.
At this point, I want to thank every single person out there that dedicated some of his precious time to create a demo video for Shellter. Thank you guys!
Last but not least, I want to thank from the bottom of my heart my friend Francisco Ribeiro (@blackthorne) for being always there for me to test the new releases of Shellter before they go public, and to provide suggestions. Thanks to his final tests, we managed to identify an issue with Stealth Mode that was caused from a payload generation issue from Metasploit. It was also because of him, continuously insisting that a RedTeam style functionality should be added in Shellter that made me finally to work on it. I can’t say how thankful I am for this.
Now get the hell out of my site, and go trick some AVs!
kyREcon