Dear friends,
We are excited to introduce Shellter Pro v3.0 (Codename: Kris Kaspersky).
Scheduled for release on: 16/2/2018
A lot of work has been put on this release, and many things have been enhanced and greatly optimized.
A huge part of this work was dedicated into enhancing further the AV evasion capabilities of Shellter Pro, thus increasing the gap between the community and the Pro editions.
Finally, we also added a series of extra features that will not just create a better user experience, but will also, in combination with the rest of the internal changes, provide a lot better AV evasion results.
So here’s a summary of what’s coming up next with the release of Shellter Pro v3.0.
Please note that the following information only provides a short overview of each new feature/update. Further technical details are available here.
- Enhanced Anti-AV Signature Technology
Several parts of the payload hiding, encoder, and obfuscation engines have been updated for this release.
These updates make writing AV signatures for Shelltered binaries an even more challenging task.
Furthermore, the updates applied to all aforementioned engines allow them to take further advantage of the overall design and architecture of the infection engine of Shellter Pro.
Putting all these together, a natural balance of binary art is created to make this version of Shellter Pro the best release ever in terms of anti-AV signatures technology. - Large Payloads Support
What about being able to inject full stageless meterpreter payloads and other custom-built DLLs without much hassle?
Now you can!
Some parts of the injection engine has been re-engineered to allow more flexibility with regards to the size of the payload(s) that can being injected into a binary. This is an optional feature and doesn’t have to be enabled all the time.
Shellter Pro will now offer the option to enable large payloads support.
In fact, you will be able to inject payloads that are up to 4MBs each, when this feature is enabled.
Well, you won’t have to use anything that big, but now you can just do it. - Upgraded Encoder
Shellter Pro will now support multiple layers of encoding for both embedded and custom payloads.
This allows the user to encode multiple times on the fly a payload during injection as there is no need to only rely on ‘Standalone Encoder’ functionality anymore for multi-layered encoding.
Furthermore, the encoding engine will now use multiple keys for each encoding layer, when DTCK is not used. - CertPlay
This feature allows Shellter Pro to save, restore, and re-use the certificates table from PE targets that are digitally signed.
Shellter Pro will now create a directory called “ShellterPro_CRTs” and will store there the certificate table of the PE file that is currently infecting, if that is signed.
By default, Shellter removes the digital signature and other artifacts from the PE header that indicate that the PE file was signed.
With this new functionality, the user is now able to optionally either restore the digital signature of the target PE file once the payload injection has been completed, and/or use the digital signature of another signed PE target that was previously saved in the aforementioned directory.
This new feature makes an infected PE file to appear as digitally signed which in many cases can increase the chances of evading certain AV products. - MSF Console Scripts Generator
This feature enhances further the automation capabilities of Shellter Pro for advanced users that enjoy using Shellter Pro via customised scripts. This feature was suggested by one of our users.
When you use some of the embedded metasploit stagers, Shellter Pro will now create an MSF console script file (.rc) which allows the user to automatically configure the listeners based on the options used during injection.
Scripts are saved inside the “ShellterPro_MSF” directory which is created in the installation directory of Shellter Pro. - Execution Flow Tracing Using Exectuable-Specific Arguments
This is an experimental feature, suggested by one of our users, that allows to trace the execution flow of an executable by using also specific arguments supported by the executable itself.
This allows to perform even more dynamic injection that can be potentially triggered only when the infected binary is launched by using the same arguments.
As you understand, this feature can be a great weapon against automatic analysis sandboxes, and AV emulation engines in general, as the payload will not be reached unless the correct arguments have been used.
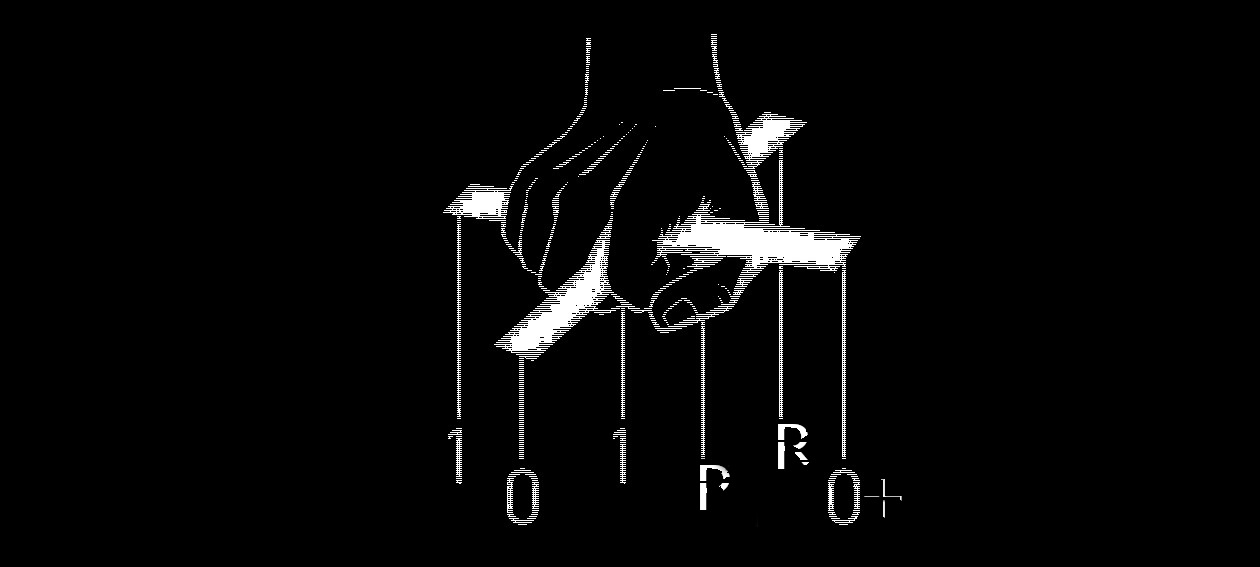
GO PRO!
Enjoy,
kyREcon